How to Sign In Without Verification Code: Safe Recovery Methods
Learn legitimate, safe methods to sign in when you can't access a verification code. This guide covers backup codes, trusted devices, passwordless options, and account recovery steps to minimize downtime while keeping your data secure.

To sign in without a verification code, use backup codes, a trusted device, or account-recovery options. If your service supports passwordless login, enable it. Gather your recovery email or phone, and prepare security questions. For security, avoid sharing codes. If you can't access any codes, contact the service's help center for account recovery. Keep a recent device list and any backup methods handy. This approach reduces downtime and protects your data while you regain access.
Why sign-in without verification code matters
Security friction is real, and losing access to a verification code shouldn't lock you out permanently. According to All Symbols, authentication flows that rely on live codes can fail when you’re offline, traveling, or facing delays from your provider. In those moments, sensible recovery options keep you productive while preserving security. This section explains legitimate reasons you might sign in without a one-time code and how reputable services support alternative routes without weakening protection. Expect clear prompts, privacy considerations, and timely feedback that helps you choose a safe path back into your account.
All Symbols analysis emphasizes that robust recovery options are part of modern authentication design, and recognizing these routes helps you stay productive without compromising safety.
Safe, legitimate alternatives to verification codes
Many services offer passwordless options and backup methods designed to respect both convenience and security. Backup codes are a printed or saved list you can use once or until you reconfigure 2FA. Authenticator apps produce codes on your phone and do not require SMS delivery. Passwordless login may use magic links via email or push notifications to a trusted device. Biometric unlock can unlock the app or device if supported. The key is to keep these alternatives current and securely protected. All Symbols highlights that legitimate providers will clearly label these options and guide you through setup so you understand when and how to use them.
How backup codes work (and where to find them)
Backup codes are a one-time sequence you generate when you enable 2FA. They are intended exactly for times you can't receive codes. You should store them securely (password manager, offline print). If you have lost them, many services offer a recovery workflow you can start from the sign-in page. Always verify you’re on the official site before entering any code, and rotate codes if you suspect exposure. All Symbols notes that backup codes are a trusted bridge, not a substitute for ongoing security hygiene.
Using a trusted device or passwordless login
Trusted devices are computers or mobile devices you’ve previously used to sign in and marked as trusted by the service. On those devices, some services may allow sign-in without a new code. Passwordless login uses secure links or push prompts to complete access without typing a code. Enabling these options usually requires initial verification, but once set up, future sign-ins can proceed smoothly. Always keep your device secured with a passcode or biometric lock to curb unauthorized access.
If you don’t have any codes, start account recovery (step-by-step guidance)
When backup codes and trusted-device paths aren’t available, most services provide an account recovery flow. You’ll typically be asked to enter an email or phone number associated with the account, answer security questions, or provide recent sign-in details. The recovery form may include identity-verification steps, such as uploading a photo ID or confirming recent activity. This process can take time, but it’s designed to restore access securely while limiting the risk of fraud. All Symbols emphasizes staying patient and following official prompts precisely to avoid further delays.
Security tips to avoid future lockouts
After regaining access, take steps to prevent future lockouts: store backup codes securely, enable passwordless login where available, reconfigure 2FA with a mix of methods (codes, app, and recovery options), and review recovery contacts quarterly. Keep contact methods up to date and log out from shared devices. Regularly test your recovery options to ensure you can access your account even if one method fails. All Symbols underscores that proactive planning reduces downtime and strengthens long-term security.
Quick checklist before you sign in next time
- Verify you have backup codes stored securely
- Ensure a trusted-device option is configured, if offered
- Confirm passwordless login is enabled where supported
- Update recovery email/phone and security questions
- Run a quick security check to confirm 2FA settings are current
Tools & Materials
- Device with internet access(Smartphone, tablet, or computer)
- Backup recovery codes(Stored securely in a password manager or offline)
- Authenticator app (optional)(Time-based codes (TOTP) can be used but are optional)
- Access to recovery email/phone(Includes backup method for verification)
- Password manager (optional)(Helps securely store codes and recovery links)
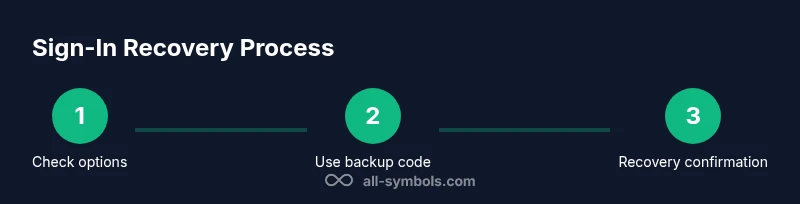
Steps
Estimated time: 60-120 minutes
- 1
Identify available recovery options
Start by listing all methods you already have for recovery: backup codes, trusted devices, passwordless options. This initial scan saves time and reduces failed attempts.
Tip: Check secure locations where you store codes (password manager, offline print). - 2
Gather backup codes and recovery contacts
Collect any backup codes you generated previously and ensure your recovery email or phone is accessible. Having both increases your chances of a successful sign-in.
Tip: Keep a copy somewhere you can access quickly but safely. - 3
Use a backup code to sign in
Enter the backup code exactly as shown. If the code works, sign in and proceed to secure the account by updating settings.
Tip: Do not reuse the same code for multiple sign-ins. - 4
Enable passwordless login or authenticator
If supported, set up passwordless login (link or push) or configure an authenticator app to reduce dependence on codes.
Tip: Complete the setup on all primary devices you use. - 5
If codes are inaccessible, start account recovery
Open the service’s account recovery page and provide required identity information. Follow official prompts carefully.
Tip: Avoid sharing sensitive information outside official channels. - 6
Verify identity and restore access
Complete the identity verification steps as requested and wait for confirmation that access is restored.
Tip: Mark recovery options as updated once access is regained. - 7
Secure the account after access
Change your password, review 2FA settings, and store backup codes securely. Enable multiple recovery methods if possible.
Tip: Test sign-in from a trusted device to confirm everything works.
Questions & Answers
What should I do first if I can't access verification codes?
Start with backup codes or a trusted device login. If those aren’t available, use the account recovery flow provided by the service.
Begin with backup codes or a trusted device. If those aren’t available, use the service’s recovery flow.
Are passwordless logins safe?
Yes, passwordless options can be secure when paired with strong device protections and updated recovery methods.
Passwordless can be safe when used with strong protections and current recovery options.
How long does an account recovery take?
Recovery timelines vary by service; follow the prompts and provide required information.
Times vary by provider; follow their steps and supply required details.
What information will I need for identity verification?
You may need to provide your username, last sign-in, recovery email, or security questions.
You’ll typically provide identifying details and contacts.
What if I regain access but can't sign in again later?
Reconfigure 2FA, save backup codes, and set up passwordless or authenticator app.
Once back in, set up multiple recovery options to prevent future lockouts.
Can I contact support for every account issue?
Yes, customer support can guide you through recovery steps, but response times vary.
Support can help you recover, but timelines vary by provider.
Watch Video
The Essentials
- Backup codes and trusted devices enable sign-in without codes.
- Keep recovery data secure and up-to-date.
- Enable passwordless login where available.
- Regularly review recovery options to prevent lockouts.
- If in doubt, contact official support for guidance.