How to Sign In Without an Authenticator App
Learn practical, safe methods to sign in when you don’t have access to an authenticator app. This guide covers backup codes, SMS/Email verification, recovery steps, and best practices to protect your account.

You can sign in without an authenticator app by using alternative verification options provided by your account: backup codes, SMS or voice verification, email verification, hardware keys, or a trusted device prompt. Start at the sign-in screen, choose the alternative verification option, and follow the on-screen prompts. If no option is visible, contact support.
Understanding sign-in without authenticator apps
Authenticator apps are a strong defense, but not always available. A modern identity setup often includes multiple fallback options you can use if you can't access your app. These options balance security with accessibility, helping you avoid lockouts while maintaining guardrails. In this section we define what 'signing in without an authenticator app' means, why providers offer fallbacks, and how to select a method that keeps your account reasonably secure while staying convenient.
Key ideas to keep in mind: backup options vary by service, some require prior configuration, and each method has its own risk profile. Understanding these trade-offs helps you choose a method that matches your needs and risk tolerance.
Common scenarios where you might skip the app
There are several real-world situations where you’ll need to sign in without an authenticator app. You might have lost your phone, switched to a new device, or be traveling without network access. In other cases, an organization may require you to use a different method when the authenticator is temporarily unavailable. Each scenario carries distinct security considerations, so pick alternatives that are reliable and reasonably secure. Be mindful of risks: SMS and email codes can be intercepted or redirected; offline backup codes stay accessible even without network, but must be stored securely; hardware keys offer strong protection but require compatibility with the service.
Backup verification options explained
Most services offer a set of fallback verification options you can configure ahead of time. Common choices include backup codes, SMS or voice codes, verification emails, and hardware security keys (FIDO2). Backup codes are offline and don’t rely on network access, but should be stored securely. SMS and email codes are convenient but susceptible to SIM swap or account compromise. Hardware keys provide strong protection but require compatible devices and service support. When selecting options, consider your environment, access frequency, and the threat model you’re protecting against.
How to set up recovery options proactively
Take a moment to configure recovery options before you need them. Generate and securely store backup codes, add a trusted phone number for SMS, set a recovery email, and, if supported, enroll a hardware security key. Keep physical backup codes in a safe place (like a locked safe) and ensure you can access the recovery email and phone when needed. Document the steps for regaining access and test the methods while you still have access.
Step-by-step paths for different providers
The exact steps vary by provider, but the general path is similar. Start at the sign-in screen, select an alternative verification method, and follow the prompts. If you selected backup codes, enter a code from your saved list. If you chose SMS or email, enter the received code. For hardware keys, insert the key when prompted. If the service requests identity verification, complete any required forms or document uploads.
Best practices for long-term security without the authenticator app
Security without an authenticator app relies on layered controls. Keep backup codes offline and updated, avoid sharing verification codes, and monitor account activity. Rotate codes regularly and ensure recovery options are reachable from trusted devices. Consider enabling multiple verification methods to reduce single points of failure and review your security settings every few months. Regular audits help you stay ahead of potential access issues without depending solely on an authenticator app.
Tools & Materials
- Backup codes (printed or securely stored)(Keep offline in a locked location)
- Phone with SMS capability(Ensure you can receive messages or calls)
- Recovery email access(Access to an alternate email for codes)
- Trusted device or browser(Optional but helpful for fewer prompts)
- Identity verification documents (if requested)(Have ready for recovery forms)
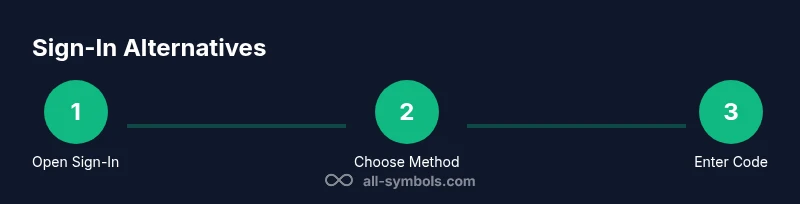
Steps
Estimated time: 25-50 minutes
- 1
Open sign-in page and access recovery options
Navigate to the sign-in page and look for a link or button that says something like 'Use another verification method' or 'I can't access my authenticator'. Click it to reveal the alternatives.
Tip: If the option isn’t visible, try a different browser or device; menus can differ between apps. - 2
Select an alternative verification method
Choose from backup codes, SMS, or email verification based on what you have configured. Some services may offer hardware keys if supported.
Tip: Have your backup options ready before you start; this reduces delays. - 3
Enter the chosen verification code
If you picked SMS or email, enter the code you received. If you used a backup code, enter one of the codes from your saved list. Codes are time- or use-bound depending on the method.
Tip: Codes can expire or be single-use; use them in one session only. - 4
If you cannot verify, start account recovery
If none of the verification methods work, initiate the account recovery flow by providing requested information and documents. This process may take time, and you may be asked to answer security questions.
Tip: Be as accurate as possible to increase recovery success. - 5
Sign in and secure your account
Once signed in, review security settings and add or update backup options to prevent future lockouts. Store backup codes securely and test access to recovery methods.
Tip: Store backup codes offline and off-device when possible. - 6
Test fallback options periodically
Periodically verify that your backup options still work to prevent surprises during an actual sign-in.
Tip: Schedule a quarterly check to maintain readiness.
Questions & Answers
Is signing in without an authenticator app safe?
Using fallback methods can be secure if they are configured properly and you keep recovery data private. Be mindful of the risks associated with SMS and email codes, and avoid sharing codes.
Fallback verification can be secure when configured correctly, but stay cautious of risks with SMS and email codes.
What should I do if I lose access to backup codes?
If backup codes are lost, use alternative options like SMS or recovery email, and contact support if those aren’t available. After regaining access, generate fresh backup codes and store them securely.
If you lose backup codes, use other verification options and contact support if needed.
Can phone verification be secure?
Phone verification is convenient but can be vulnerable to SIM swap attacks. Prefer tying codes to multiple options and avoid relying on a single channel.
Phone codes are convenient but can be risky; use additional methods when possible.
What if I can’t sign in at all?
If you can’t complete any verification method, start the account recovery process by providing identity verification details and any requested documentation. This may take time, but is often effective.
If you can’t verify, start the recovery process with the information the provider asks for.
How should I set up backup options securely?
Configure backup codes, add recovery email and phone, and consider a hardware key if supported. Store codes offline and review settings periodically for security.
Set up backups like codes and recovery options, and review security settings regularly.
Are there better practices for ongoing account security?
Maintain multiple verification options, monitor account activity, and avoid sharing verification details. Regularly update security settings and perform periodic audits.
Keep multiple verification options and monitor activity for ongoing security.
Watch Video
The Essentials
- Identify available fallback verification options.
- Configure backup codes and recovery options before you need them.
- Use multiple verification paths to reduce lockout risk.
- Test recovery options periodically to ensure accessibility.
- Keep sensitive recovery data offline and secure.